
Computers and Technology, 01.04.2020 03:14 deisyy101
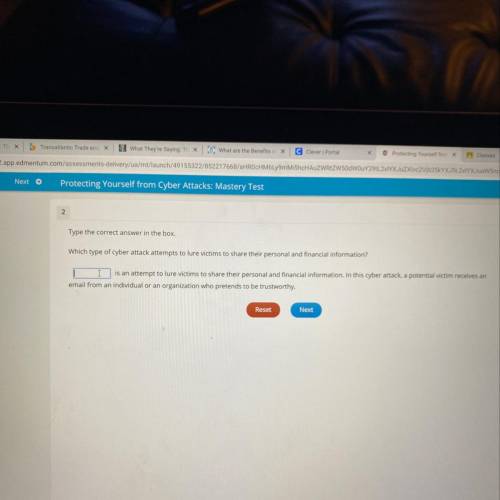
Which type of cyber attack attempts to lure victims to share their personal and financial information?

Answers: 3
Another question on Computers and Technology

Computers and Technology, 22.06.2019 15:30
Melissa needs to add a topic to an email that she will send to her teacher. choose the name of the field where she should type her topic.
Answers: 2

Computers and Technology, 23.06.2019 00:20
The open systems interconnection (osi) reference model: defines standards for many aspects of computing and communications within a network. is a generic description for how computers use multiple layers of protocol rules to communicate across a network. defines standards for wireless local area network (wlan) communication protocols. details the advantages and disadvantages of various basic network cabling options.
Answers: 1

Computers and Technology, 23.06.2019 11:00
This chapter lists many ways in which becoming computer literate is beneficial. think about what your life will be like once you’re started in your career. what areas of computing will be most important for you to understand? how would an understanding of computer hardware and software you in working from home, working with groups in other countries and contributing your talents.
Answers: 1

Computers and Technology, 23.06.2019 22:30
Apart from confidential information, what other information does nda to outline? ndas not only outline confidential information, but they also enable you to outline .
Answers: 1
You know the right answer?
Which type of cyber attack attempts to lure victims to share their personal and financial informatio...
Questions

Arts, 18.03.2021 03:30



Social Studies, 18.03.2021 03:30

Social Studies, 18.03.2021 03:30

Mathematics, 18.03.2021 03:30

English, 18.03.2021 03:30


Mathematics, 18.03.2021 03:30


Mathematics, 18.03.2021 03:30

Chemistry, 18.03.2021 03:30


History, 18.03.2021 03:30



Mathematics, 18.03.2021 03:30

English, 18.03.2021 03:30

Mathematics, 18.03.2021 03:30



