Computers and Technology, 18.04.2020 04:37 sadcase85
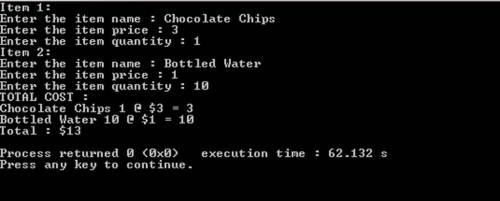
30.1 LAB*: Warm up: Online shopping cart (Part 1) (1) Create three files to submit: ItemToPurchase. h - Class declaration ItemToPurchase. cpp - Class definition main. cpp - main() function Build the ItemToPurchase class with the following specifications: Default constructor Public class functions (mutators & accessors) SetName() & GetName() (2 pts) SetPrice() & GetPrice() (2 pts) SetQuantity() & GetQuantity() (2 pts) Private data members string itemName - Initialized in default constructor to "none" int itemPrice - Initialized in default constructor to 0 int itemQuantity - Initialized in default constructor to 0 (2) In main(), prompt the user for two items and create two objects of the ItemToPurchase class. Before prompting for the second item, call cin. ignore() to allow the user to input a new string. (2 pts)

Answers: 3
Another question on Computers and Technology

Computers and Technology, 22.06.2019 21:30
Elements such as fonts colors visual structure graphics and the interface of a web page should complement each other to ensure blank
Answers: 3

Computers and Technology, 23.06.2019 22:30
You draw two cards from a standard deck of 52 cards, but before you draw the second card, you put the first one back and reshuffle the deck. (a) are the outcomes on the two cards independent? why?
Answers: 3

Computers and Technology, 24.06.2019 15:00
Universal windows platform is designed for which windows 10 version?
Answers: 1

Computers and Technology, 24.06.2019 15:20
Local area networks use many of the same network technologies and the internet, only on a smaller scale. devices that access lans are equipped with a network interface that contains circuitry for wireless or wired connections. devices also have a physical address, in addition to the ip addresses acquired from a dhcp server. the most popular wired technology is . the most popular wireless technology is , which can be configured as a(n) or star topology. setting up a lan and configuring its router is fairly easy. the first step is to change the standard to one that is secure. next, create a(n) that uniquely identifies the network by name. it is also important to activate wireless to prevent wireless signals from being intercepted during transmission. a limited-access network can be created for visitors to use. by activating , the router will be able to assign ip addresses to each device that joins the network. to connect to a secure lan that is protected by encryption, an encryption , or password, is required. lans can be used to access data collected by iot devices and the networks that tie these devices together. technologies such as rfid, nfc, bluetooth smart, zigbee, and z-wave offer -power links, essential for battery-powered devices that can’t expend excess amounts of energy transmitting data.
Answers: 1
You know the right answer?
30.1 LAB*: Warm up: Online shopping cart (Part 1) (1) Create three files to submit: ItemToPurchase....
Questions





Mathematics, 09.01.2020 00:31


History, 09.01.2020 00:31

Computers and Technology, 09.01.2020 00:31


Health, 09.01.2020 00:31


Mathematics, 09.01.2020 00:31

Mathematics, 09.01.2020 00:31




English, 09.01.2020 00:31


Mathematics, 09.01.2020 00:31