
Computers and Technology, 27.04.2021 19:00 codylowery5635
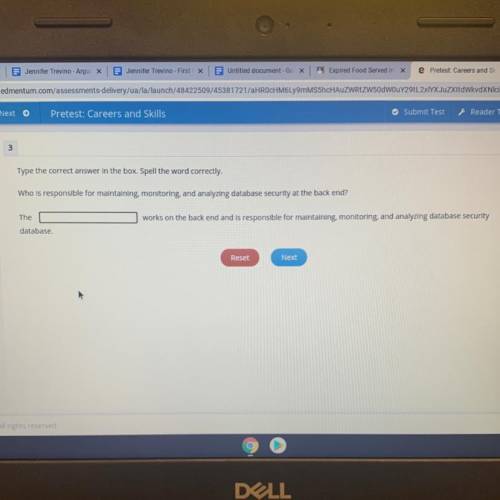
Who is responsible for maintaining, monitoring, and analyzing database security at the back end?
The
works on the back end and is responsible for maintaining, monitoring, and analyzing database security
database.

Answers: 1
Another question on Computers and Technology

Computers and Technology, 22.06.2019 01:00
Ap practice - performance task response the ap create performance task asks you to write about an abstraction that you developed and wrote into your code. most of the time that means identifying a function or procedure you wrote to "manage complexity" in your program. here is the actual prompt from the create performance task: 2d. capture and paste a program code segment that contains an abstraction you developed individually on your own (marked with a rectangle). this abstraction must integrate mathematical and logical concepts. explain how your abstraction manage the complexity of your program. (must not exceed 200 words) below is a segment of code from an "under the sea" program with a rectangle drawn around a portion of the code identifying an abstraction. imagine that you wrote this and are composing an ap response about how this abstraction manages complexity. (note: ignore the requirement that the abstraction integrate "mathematical and logical concepts" for this practice response. just write about managing complexity). explain how the abstraction marked with the rectangle in the code above manage complexity of this program. write your response here submit
Answers: 2

Computers and Technology, 24.06.2019 11:00
Which of the statements below describe the guidelines for the use of text in presentation programs? a. do not use numbered lists. b. fonts should be appropriate for your audience. c. limit the number of fonts you use to three or four. d. only use bulleted lists for sales promotions. e. select font sizes that are appropriate for your delivery method. f. use font colors that work well with your background. select all that apply
Answers: 1

Computers and Technology, 24.06.2019 16:00
Which of the following characters is acceptable to use in a filename? ? / – %
Answers: 1

Computers and Technology, 25.06.2019 00:00
One difference of input method between most desktop computers and most tablets is the memory the touch screen the speech recognition
Answers: 1
You know the right answer?
Who is responsible for maintaining, monitoring, and analyzing database security at the back end?
T...
Questions


History, 18.11.2020 23:40


Chemistry, 18.11.2020 23:40



English, 18.11.2020 23:40

Mathematics, 18.11.2020 23:40

History, 18.11.2020 23:40

Computers and Technology, 18.11.2020 23:40




Physics, 18.11.2020 23:40


History, 18.11.2020 23:40

History, 18.11.2020 23:40

Mathematics, 18.11.2020 23:40


Mathematics, 18.11.2020 23:40



