Answers: 3
Another question on Computers and Technology

Computers and Technology, 22.06.2019 10:10
3. bob is arguing that if you use output feedback (ofb) mode twice in a row to encrypt a long message, m, using the same key each time, it will be more secure. explain why bob is wrong, no matter what encryption algorithm he is using for block encryption (15 points).
Answers: 3

Computers and Technology, 23.06.2019 13:30
Spoons are designed to be used for: spring hammering. applying body filler. identifying high and low spots. sanding highly formed areas.
Answers: 3

Computers and Technology, 23.06.2019 14:30
Select the correct answer. a company wants to use online methods to target more customers. it decides to conduct a market research by collecting the data of a few customers with their consent. they want to track data of the sites that their customers frequently visit. which software can the company? a. spyware b. bots c. adware d. trojan horse e. rootkits
Answers: 1

Computers and Technology, 23.06.2019 20:00
Me ajude por favor , coloquei uma senha e não consigo tira-la no chorme
Answers: 2
You know the right answer?
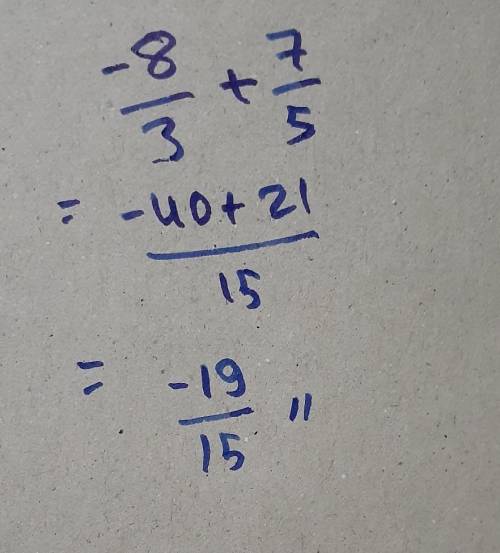
Solve(-8/3)+7/5 please answer...
Questions

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Social Studies, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Social Studies, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01

Mathematics, 18.09.2020 14:01