Aa
...

Answers: 2
Another question on Computers and Technology

Computers and Technology, 21.06.2019 21:30
Asuccessful format string attack attempted to steal user account information by reading from unauthorized memory. answer the followings with proper explanation a)this attack will lead to violation of which security policies?
Answers: 2

Computers and Technology, 22.06.2019 11:00
Which action is good business etiquette? a. switching your cell phone off before you enter a meeting b. keeping your cell phone on low volume before you enter a meeting c. setting a pleasant ring tone on your cell phone before you enter a meeting d. setting a standard ringtone on your cell phone before you enter a meeting
Answers: 1

Computers and Technology, 23.06.2019 08:00
The managing director of a company sends a christmas greeting to all his employees through the company email. which type of network does he use? he uses an .
Answers: 3

Computers and Technology, 24.06.2019 03:00
Using a conditional expression, write a statement that increments numusers if updatedirection is 1, otherwise decrements numusers. ex: if numusers is 8 and updatedirection is 1, numusers becomes 9; if updatedirection is 0, numusers becomes 7.
Answers: 1
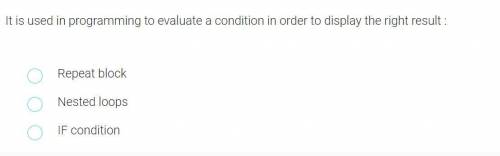
You know the right answer?
Questions







Mathematics, 20.11.2020 16:40

History, 20.11.2020 16:40



Computers and Technology, 20.11.2020 16:40

Computers and Technology, 20.11.2020 16:40



Mathematics, 20.11.2020 16:40

Mathematics, 20.11.2020 16:40