
Computers and Technology, 12.12.2020 16:00 addison62
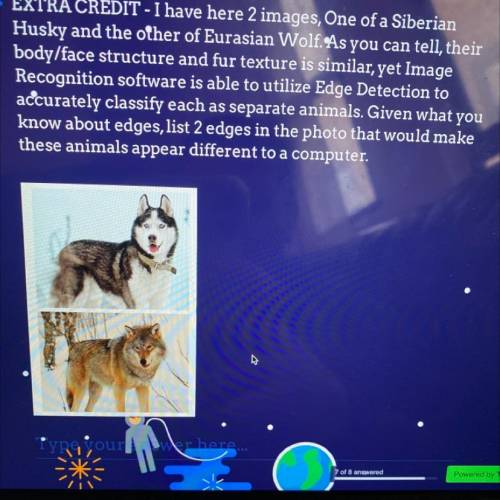
EXTRA CREDIT - I have here 2 images, One of a Siberian
Husky and the other of Eurasian Wolf. As you can tell, their
body/face structure and fur texture is similar, yet Image
Recognition software is able to utilize Edge Detection to
accurately classify each as separate animals. Given what you
know about edges, list 2 edges in the photo that would make
these animals appear different to a computer.

Answers: 2
Another question on Computers and Technology

Computers and Technology, 22.06.2019 09:40
It is vital to research each of the services you plan to disable before implementing any change, especially on critical machines such as the: a. servers in the test environment. b. domain controller and other infrastructure servers. c. desktops that have previously been attacked. d. desktops used by upper-level management.
Answers: 2

Computers and Technology, 23.06.2019 18:30
Where can page numbers appear? check all that apply. in the header inside tables in the footer at the bottom of columns at the top of columns
Answers: 1

Computers and Technology, 24.06.2019 00:30
Asecurity policy is a a. set of guidlines b. set of transmission protocols c. written document d. set of rules based on standards and guidelines
Answers: 2

Computers and Technology, 24.06.2019 07:30
Consider the folloeing website url: what does the "http: //" represent? a. protocal identifier. b. ftp. c. domain name d. resource name
Answers: 2
You know the right answer?
EXTRA CREDIT - I have here 2 images, One of a Siberian
Husky and the other of Eurasian Wolf. As you...
Questions

Mathematics, 28.11.2019 02:31


Social Studies, 28.11.2019 02:31







Mathematics, 28.11.2019 02:31


Mathematics, 28.11.2019 02:31

Mathematics, 28.11.2019 02:31


History, 28.11.2019 02:31

Chemistry, 28.11.2019 02:31


History, 28.11.2019 02:31


Mathematics, 28.11.2019 02:31



